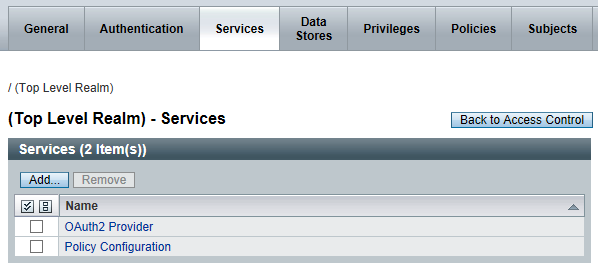
Recently, we have a customer who wants to extend their OpenAM infrastructure to mobile applications. That should not be a problem at all since OpenAM supports OAuth2 Provider since version 10.1.0-Express.
In addition, customer wants to allow mobile users to authenticate using Facebook and/or on-premise LDAP. Well, OpenAM does support OAuth2 authentication module which acts as an OAuth2 Client to Facebook (which acts as an OAuth2 authorization server).
So, we spent some time exploring the possibility of having OpenAM acts as an OAuth2 Provider and OAuth2 Client.
1. Basically, all mobile applications are to authenticate via OpenAM OAuth2 Provider, instead of directly with Facebook.
2. OpenAM Login Page allows Facebook OAuth2 authentication or LDAP authentication (as per requirement). Of course, the Login Page might need to customize to render nicely on mobile phones.
3. User clicks Facebook OAuth2 authentication on OpenAM Login Page (notice this trigger a link from OpenAM server to Facebook; not mobile applications with Facebook directly). What actually happens is a redirection from OpenAM Login Page to Facebook application on the same mobile device.
4. Upon successful authentication (which should be seamless on mobile phones since users seldom log out from Facebook app), Facebook OAuth2 token is returned to OpenAM server. This establish a valid session in OpenAM.
5. OpenAM now returns its own OAuth2 token back to the mobile application. (instead of a OAuth2 token from Facebook)
One might ask what's the rationale for doing so? Isn't it more straight-forward for the mobile applications to authenticate directly with Facebook?
Well, the real business case is the customer wants to add more Social Logins in the near future. e.g. Google, Yahoo, etc... With this implementation, there is no need for any modification on the mobile applications as and when a new Social Login is added.
Nice, isn't it?
.